Where's the Nigerian Prince Now? He Grew Up and Stole Your Retirement Fund
Trace the evolution of the classic advance-fee scam from its fax-machine origins through its email heyday to its
story telling · 10 min read · April 2026

The Email You Deleted—And What It Became
You remember the email. Maybe it arrived in 2003, maybe 2009—the timestamp barely matters because it was always the same fever dream: an ALL CAPS subject line, a deposed royal or grieving widow, a fortune somewhere between $18 and $47 million in a frozen account, and you—specifically you, a trustworthy stranger—selected to help move it. In exchange for your bank details and a small "processing fee," you'd receive a generous cut.
We laughed. We forwarded it to friends as a joke. We felt briefly, pleasurably superior to whoever might actually fall for something so cartoonishly obvious.
Here's what we missed while we were busy feeling smug: the people writing those emails were running an experiment. Every reply was data. Every wired fee was proof of concept. The clumsy grammar and absurd premise weren't accidents—they were filters, designed to find the most persuadable people in the largest possible pool. The Nigerian prince scam wasn't the con. It was the prototype.
Because that laughably crude email was the larval stage of something that would eventually cost Americans alone billions of dollars annually—sleeker, more patient, and far more personal.
So where did the prince go? And what, exactly, did he become?
Before the Email: The Scam's Surprisingly Long Childhood
Here's the thing that should reframe everything you think you know about the "Nigerian prince" email: by the time it landed in your inbox, it was already ancient.
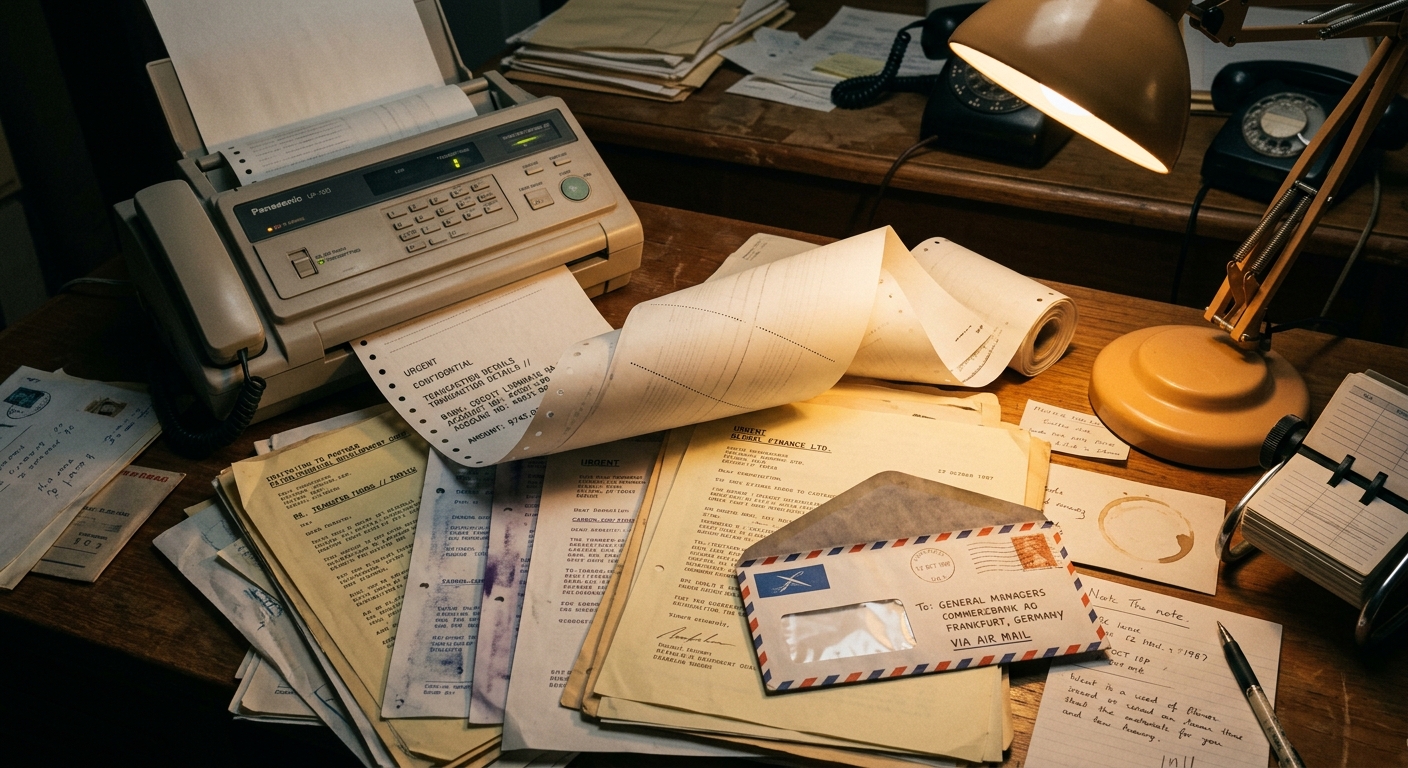
The con has a proper legal name—the 419 scam, after Section 419 of the Nigerian Criminal Code, which outlaws obtaining property by false pretenses. But Nigerian prosecutors were chasing these schemes long before the internet existed, because the original versions ran on paper. Physical letters. Fax machines. In the 1980s and early 1990s, operators in Lagos would blast thousands of faxes to Western businesses, pitching the same basic story: there's a fortune trapped somewhere, you're the chosen partner to help move it, and all you need to do is front a small fee to unlock the windfall.
The core mechanic is almost insultingly simple: promise an enormous reward, require a modest upfront payment to release it, then manufacture endless new fees until the victim runs dry or wises up. That's it. That's the whole trick.
What's genuinely staggering is how old that trick is. Historians trace a near-identical scheme called the "Spanish Prisoner" con back to the 1500s, with documented versions circulating through Europe well into the 1800s. The letter changed—a nobleman trapped by the Inquisition was replaced by an oil minister's widow—but the psychological blueprint was identical.
Nigeria didn't invent this psychology. What it contributed was geography and timing. After the oil-boom collapse of the early 1980s devastated the Nigerian economy, a generation of educated, entrepreneurial young men found themselves with ambition, no legitimate outlets, and—crucially—early access to telecommunications infrastructure in Lagos. The fax machine was their first weapon. The internet would hand them something far more powerful.
The Golden Age of Obvious Fraud (And Why It Worked Anyway)
Then the internet arrived, and everything scaled.
What had been a labor-intensive postal hustle—printing letters, buying stamps, waiting weeks for a mark to write back—became essentially free to operate overnight. By the late 1990s, a single operator could blast millions of emails in an afternoon for the cost of a dial-up connection. Volume wasn't a side effect of the business model; volume was the business model. If one person in ten thousand replied, that was a good day's work.
Here's the part that still trips people up: the terrible spelling, the baroque premise about a deposed general's oil fortune—some of that was deliberate. As a Microsoft researcher named Cormac Herley famously argued, the outrageous implausibility functioned as a self-selecting filter. Skeptics would delete the email immediately, which was fine. The scammers didn't want skeptics. They wanted the small percentage of readers credulous enough—or desperate enough, or lonely enough—to write back. Filtering out the savvy early saved everyone time.
And the people who did write back? Not the profile you'd expect. Yes, some were elderly or unsophisticated. But investigators and journalists who interviewed victims consistently found people who were grieving, financially underwater after a medical crisis, or simply carrying the very human conviction that this time something good was finally happening to them. Greed played a role, sure—the premise always involved a cut of the fortune—but so did loneliness, hope, and the particular vulnerability of someone who really needed a windfall to be real.
The money was staggering. Even as "Nigerian prince" became a punchline, the FBI and FTC documented hundreds of millions of dollars in annual losses to this kind of advance-fee fraud at its peak. The joke hadn't killed the scam. It had just made victims too embarrassed to report it.
Meanwhile, the scammers were taking notes. Every reply was a data point, every successful extraction a template, every failure a lesson in what to tighten next. They were, in the most unsettling sense, learning.

Puberty: When the Scam Got Smarter and Stopped Being Funny
The golden age of the Nigerian prince email couldn't last. As spam filters got sharper and "DELETE—IT'S A SCAM" became a cultural reflex, the blunt-force volume model started hemorrhaging returns. Sending a million badly-spelled emails to collect a few thousand dollars was no longer good business. The scam had to grow up.
And grow up it did—in two distinct directions.
The first was Business Email Compromise, or BEC. Instead of targeting retired schoolteachers, operators went after companies—impersonating CEOs, CFOs, or trusted vendors to redirect wire transfers into accounts they controlled. The FBI's Internet Crime Complaint Center has tracked BEC losses in the tens of billions of dollars globally over the past decade, making it one of the costliest fraud categories in existence. No princes, no inheritance stories. Just a convincing email from "the boss" asking accounting to process an urgent payment.
The second evolution was slower, more patient, and in some ways more disturbing: the romance scam. Forget the one-email pitch. This version plays out over weeks or months—a relationship built through daily messages, shared jokes, maybe even video calls. By the time money enters the conversation, the victim isn't wiring funds to a stranger. They're helping someone they love.
Both shifts reflect the same core strategic pivot: stop broadcasting to thousands hoping one bites, and start investing in one target at a time for a dramatically larger payout. It's the difference between fishing with a net and hunting with a rifle.
And as the strategy shifted, the geography was quietly expanding. Nigeria remained significant, but scam infrastructure spread into Ghana, South Africa, and eventually—with devastating efficiency—into Southeast Asia, where an entirely new chapter was being written.

The Apex Predator: Pig Butchering and the Romance-Crypto Hybrid
If the advance-fee scam is a smash-and-grab, pig butchering is a long con so patient it borders on the artistic—in the most disturbing possible sense.
The name comes from Chinese: sha zhu pan, literally "pig butchering plate." The metaphor is uncomfortably precise. You don't rush a pig to slaughter. You fatten it first. In this context, you are the pig, and the fattening process can take weeks or months of what feels like genuine human connection—a wrong-number text that blossoms into daily conversation, a LinkedIn introduction from an attractive stranger who seems professionally impressive, a dating app match who never quite pushes toward meeting in person but always has time to talk. The relationship feels real because the scammer's investment in it is real, in a calculated, mercenary way.
Then, almost as an afterthought, your new friend mentions crypto. They've been doing well with a particular platform—nothing pushy, just sharing. You try it with a small amount. You withdraw a little profit, no problem. The trap has a door that opens from the inside, which is exactly what makes it so effective. Deposits escalate. Then one day the platform develops a "tax issue" requiring one final payment to release your funds, and then—nothing. Your friend is gone. The platform is gone. The money is gone.
In 2023 alone, the FBI's Internet Crime Report tracked over $3.5 billion in American losses to investment fraud, with pig butchering schemes accounting for a massive and growing share. This is not a story about unusually gullible people. These operations employ professional psychologists, run A/B tests on manipulation scripts, and maintain shift schedules. It's a psychological operation with a balance sheet.
Crypto isn't incidental to any of this—it's load-bearing. Transactions are irreversible by design, pseudonymous by architecture, and wrapped in enough gold-rush excitement that moving large sums feels like bold investing rather than obvious danger.
There's one more layer that makes this story genuinely harrowing: many of the people running these scripts are themselves victims. Trafficked into scam compounds across Myanmar, Cambodia, and Laos, they work under threat of violence—turning a financial crime story into a human rights emergency that investigators are only beginning to fully reckon with.

The Constant: Why the Same Brain Glitch Gets Exploited Every Time
The unnerving constant, across 500 years and every new platform, is not the technology. It's the same set of human levers: hope, trust, and sunk cost. Once you've invested money, time, secrets, or your whole heart, walking away doesn't feel like prudence. It feels like making the loss official.
That's why romance scams can resemble the tactics used in coercive groups: first comes overwhelming attention, constant contact, and the eerie sense that someone finally, perfectly gets you. Then come isolation, urgency, and a slow transfer of trust from your own judgment to theirs. As the FTC warns about romance scams, the emotional connection is the point; the money request comes later, after the bond is doing the heavy lifting.
And smart people get caught because intelligence is not a force field. Stress narrows attention. Loneliness makes connection feel precious. Big life transitions—divorce, grief, retirement, illness, a move—can lower the mind's usual defenses at exactly the wrong moment. Federal investigators repeatedly note that fraud victims cut across all age, income, and education levels. This is not about stupidity. It's about human vulnerability meeting a practiced script.
Then there's shame, the scammer's silent accomplice. Many victims never report because admitting what happened can feel almost worse than the theft itself. Fraudsters count on that reflex. Naming it matters, because shame doesn't just hide the crime. It helps the next one happen.
How to Spot the Prince in His New Clothes
The scam has changed its costume, but the seams still show—if you know where to look.
A few red flags cut across virtually every modern variant. The contact is always unsolicited. The emotional intimacy arrives suspiciously fast—declarations of connection within days, sometimes hours. Any investment opportunity introduced by a romantic or new online contact is, full stop, a warning sign worth treating as disqualifying. And there's almost always pressure to migrate off the dating app or social platform onto WhatsApp or Telegram, where conversations leave fewer corporate footprints.
One trick worth memorizing is the test withdrawal. Early in the relationship, the platform will let you pull out a small amount—say, $200—to "prove" everything is legitimate. It works. The money arrives. You relax. Then you deposit serious money, and suddenly your account is frozen pending "taxes" or "verification fees." That $200 was an investment in your trust, and it paid off handsomely for them.
The fastest countermeasure costs you 90 seconds: reverse image search every profile photo. Drag the image into Google Images or TinEye. If that glamorous offshore engineer's headshot belongs to a Finnish fitness influencer, you have your answer.
If you've been targeted—whether you lost money or not—report it. The FBI's Internet Crime Complaint Center (IC3) and the FTC's ReportFraud portal both accept complaints. Recovery is rarely guaranteed, but every report feeds the pattern data that helps investigators connect operations across dozens of victims and, occasionally, dismantle entire networks.
The tools exist. The scam just counts on you not using them.
The Prince Is Very Much Alive
Here's the thing about that ridiculous email—the broken English, the implausible royalty, the bank account number sitting right there in paragraph three. It wasn't the embarrassing opening act of a dead-end con. It was kindergarten. It was the industry learning to walk before it learned to run your retirement savings into a fake crypto exchange.
That clunky message was the awkward adolescence of what is now, by any honest accounting, a criminal enterprise that rivals legitimate Fortune 500 companies in revenue—built not on a flaw in technology, but on a flaw that isn't a flaw at all. Loneliness is human. Hope is human. The instinct to trust someone who seems to trust you first? Profoundly, stubbornly human. The scam didn't survive decades by getting lucky. It survived by getting smarter about us.
Which means the only real armor is the playbook itself—and now you have it.
There's something worth sitting with here, beyond the warnings. The audacity of the evolution is, genuinely, staggering. From a photocopied fax to an AI-generated suitor with a backstory, a face, and six weeks of your Tuesday evenings. Whoever the prince was, he's long gone—replaced by an entire industry of people who studied what made him work and built an empire on the answer.
Know the moves. That's the whole game.